Messages that can never be read by anyone else
Not by hackers. Not by governments. Not by us. Not even with future technology.
ASH uses the only encryption method that's mathematically proven to be unbreakable. It's called a One-Time Pad, and it's been trusted for the most sensitive communications since World War I.
Why is ASH different?
Other "Secure" Apps
Apps like Signal and WhatsApp use encryption that's "very hard" to break. But "very hard" isn't impossible. With enough computing power or future technology (like quantum computers), these messages could potentially be decrypted.
Think of it like a really complicated lock. Today's lockpicks can't open it, but someone might invent a better lockpick tomorrow.
ASH's Approach
ASH uses a One-Time Pad, which is mathematically proven to be unbreakable. Not "really hard to break" — actually, genuinely impossible. No amount of computing power, time, or future technology can crack it.
Think of it like burning the message after reading. There's nothing left to decrypt, no matter how good your tools are.
This isn't marketing speak. It's mathematics. The proof was published by Claude Shannon (the father of information theory) in 1949, and it's still uncontested.
Four steps to unbreakable privacy
ASH requires a bit more effort than regular messaging apps. But that effort is what makes it truly secure.
Create the Pad
Meet your contact in person. One device initiates and generates the One-Time Pad — the encryption key you'll share.
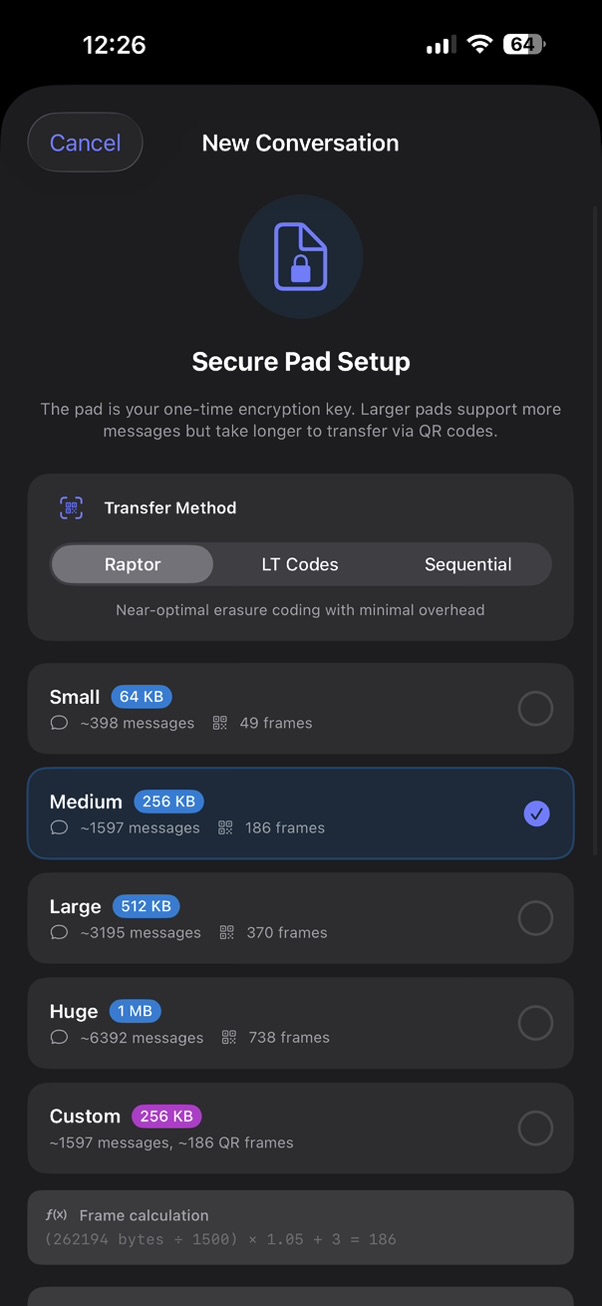
Choose pad size based on how many messages you need. Larger pads allow more messages but take longer to transfer.
How pad usage works: Each message consumes about 100 bytes of your pad — 64 bytes for authentication, plus your message length (minimum 32 bytes).
A 256 KB pad gives you ~1,500 messages. A short "OK" uses the same minimum as a longer text up to 32 characters.

Transfer via QR
The initiator displays streaming QR codes while the receiver scans them. The key transfers directly between devices — never touching the internet.
Both devices then display a 6-word phrase. Verify they match out loud to confirm the transfer was successful.
Send Messages
Message normally through the app. Each message uses up a tiny piece of your shared key, and that piece is destroyed forever after use.
Depending on key size, you can send hundreds to thousands of messages. Track your remaining pad in the conversation view.


Burn When Done
When you're finished, burn the conversation. All remaining key material is destroyed, making it mathematically impossible to recover any messages.
Gone forever. No backups. No traces. No one — not even with a court order — can ever read those messages.
Watch real encryption happen
This interactive demo shows exactly how ASH encrypts messages. Type a message and watch it get encrypted using a real One-Time Pad.
This runs the real ASH cryptographic code in your browser
Shared One-Time Pad
1 KB pad • Each message: 64B auth + 32B min encrypted
Both parties read these 6 words aloud to confirm identical pads:
If words match, pads are identical. If different, ceremony failed — discard and retry.
Alice (Initiator)
Encrypts from pad start →
Bob (Responder)
← Encrypts from pad end
How authenticated encryption works
Authentication key (64B). Each message uses a 64-byte Wegman-Carter authentication key for a 256-bit MAC. This ensures message integrity — any tampering is detected.
Encryption key (32B). The message is padded to 32 bytes minimum, then XOR'd with unique pad bytes. OTP encryption is mathematically unbreakable when keys are truly random and never reused.
Verify-then-decrypt. Receivers verify the MAC before decryption. If the tag doesn't match, the message is rejected — preventing any oracle attacks on the ciphertext.
When regular encryption isn't enough
ASH isn't for everyday chatting — that's what Signal is for. ASH is for when the stakes are high and you need absolute certainty.
Journalists
Protecting sources who risk everything to share information. When a source's safety depends on secrecy, "probably secure" isn't good enough.
Whistleblowers
Exposing wrongdoing while protecting yourself. When you're revealing secrets, you need communication that can't be compromised — even years later.
Human Rights Workers
Operating in dangerous environments where surveillance is a matter of life and death. Activists and advocates need guarantees, not promises.
Sensitive Business
Deals, negotiations, and strategic discussions where leaks could cost millions. When confidentiality is everything, absolute security matters.
Common Questions
Why do I have to meet in person?
This is the key to everything. When you share keys over the internet (like other apps do), someone could potentially intercept them. By meeting in person:
- You know exactly who you're sharing keys with
- The keys never touch the internet
- No one can intercept what doesn't travel over wires
Yes, it's less convenient. But that inconvenience is exactly what makes ASH unbreakable.
Why can I only send a limited number of messages?
One-Time Pad encryption requires that you use a unique piece of key for every byte of your message. Once that piece is used, it's destroyed forever.
When you set up ASH, you choose how much key material to create:
- 64KB — About 25 messages (quick conversations)
- 256KB — About 200 messages (extended communication)
- 1MB — About 800 messages (long-term contact)
When you run out, you meet again to create a new key. This limitation is what makes the security mathematically perfect.
What if I lose my phone?
If you lose your phone, your keys are gone. This is by design — there's no "forgot password" or cloud backup.
Here's what happens:
- You can't read old messages (they're gone with the key)
- No one else can read them either (they'd need the same key)
- You'll need to meet your contact again to establish a new connection
This might seem harsh, but it's actually a security feature. There's no way for anyone — including us — to recover your messages.
Is ASH really more secure than Signal?
Signal is an excellent app with very strong security — we recommend it for everyday use. The difference is in the type of security:
Signal's Security
Based on math problems that are "extremely hard" to solve. Secure against today's computers, but potentially vulnerable to future quantum computers.
ASH's Security
Based on mathematical proof that breaking it is impossible — not hard, impossible. Secure against any computer, forever.
For most people, Signal is perfect. ASH is for situations where you can't accept any risk at all.
What about photos and videos?
ASH only supports text messages and location sharing. Here's why:
- A single photo could be 5MB — that's more than your entire key
- A video would exhaust your key almost instantly
- Text is what matters most for sensitive communication
If you need to share files, use a different secure method. ASH is focused on doing one thing perfectly: secure text messaging.
Can the government force you to decrypt messages?
If you still have the key on your device, you could theoretically be compelled to decrypt messages (laws vary by country).
However, once you "burn" a conversation:
- The key is destroyed
- You physically cannot decrypt the messages
- No legal demand can make the impossible possible
This is why the burn feature exists — it's not just about privacy, it's about making sure messages can never be recovered by anyone.
What ASH protects
ASH provides specific, provable security guarantees. Not marketing claims — mathematical facts.
Perfect Secrecy
Your encrypted message reveals absolutely nothing about the original content. This is mathematically proven — not just "very secure."
Future-Proof
Quantum computers will break most encryption. ASH is completely immune because it doesn't rely on hard math problems — it's provably unbreakable.
No Server Access
Our servers never see your messages or keys. They just pass along encrypted data that looks like random noise to everyone — including us.
Forward Secrecy
Each message uses unique key bytes that are destroyed after use. Even if someone gets your phone tomorrow, they can't read today's messages.
No Backdoors
There's no master key, no recovery option, no way for us (or anyone) to access your messages. The math doesn't allow it.
Open Source
The encryption code is public on GitHub. Security researchers can verify every claim we make. Trust, but verify.
The trade-offs
Perfect security requires real limitations. We believe in being upfront about them.
You must meet in person
This is the foundation of security. If you can't meet someone face-to-face, you can't use ASH with them. It's inconvenient, but it's what makes everything else possible.
Limited message capacity
You can send 25-800 messages before needing to meet again and create a new key. This isn't a bug — it's how One-Time Pad encryption works.
One-to-one only
No group chats. Each conversation is between exactly two people. Groups would require sharing keys with multiple people, which weakens security exponentially.
Text only
No photos, videos, or file attachments — they'd use up your key too quickly. ASH is for important text conversations, not media sharing.
No recovery possible
If you lose your phone or delete the app, your keys and messages are gone forever. There's no backup, no recovery, no "forgot password." This is a feature, not a bug.
Ready for true privacy?
Download ASH and meet someone to establish your first unbreakable conversation.
Free. No ads. No tracking. Open source.